Buggy Law 2: eIDAS Without Digital DNA
Can legislation have bugs? That is, can it contain “errors or imperfections that reduce reliability, performance, or user experience” – just like bugs do in computer software? In this post we will find out more about how eIDAS handles digital DNA. eIDAS is the EU law that controls online identification and online signatures for the public sector in all EU states.
Digital DNA
In the previous post we coined the term “digital DNA” – something that, just like ordinary DNA, creates such a strong link to you that you cannot plausibly deny it. When you sign a document online your digital DNA is attached to that document.
Digital DNA is technically a cryptographically assured link. It’s modern computer security. It’s based on encryption. State of the art computer security insists: forget obfuscation and concealment to protect your computing secrets. Digital DNA is the way to go, it’s state of the art.
Who Signed, Really?
In the second example in the previous post we submitted an income statement online to the Swedish Tax Agency. To our surprise we did so, and had it accepted, without ever signing anything. To sign without signing? The explanation is that eIDAS supports a type of signature called qualified signatures. They are supposed to offer the greatest legal protection in the eIDAS inventory.
We cannot be sure that what we saw at the Swedish Tax Agency was formally a qualified signature according to eIDAS. What we saw was, in any case, a procedure based on a similar theory.
The theory is that a signature robot can be trusted to sign on your behalf. A signature created this way will contain the digital DNA of the signature robot. All would be well if your own digital DNA was also included in some way, but it isn’t.

The Robot That Signs For You
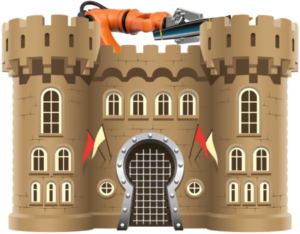
Isn’t it risky to relinquish one’s signing authority to a robot? The remedy proposed by eIDAS is to surround the robot with strong security. What you get is a “robot in a fortress”. The technical term used by eIDAS is a qualified electronic signature creation device, a mouthful that may be abbreviated QESCD.
If you are the person who is requested to sign (the signatory) you actually don’t have to sign anything. You only go through additional online identification. Identification does not transmit your digital DNA and thus the resulting signature does not contain your digital DNA. There is no cryptographically assured link from the signature back to you.
The idea is that strong security requirements on the QESCD makes up for the lack of your digital DNA. What eIDAS does is effectively to use obfuscation and concealment instead of encryption (your digital DNA). This is “security by obscurity” and is not state of the art.
Imagine Fort Knox in the USA. Supposedly it contains enormous amounts of gold under extreme protection. Imagine putting a crate of bricks into one of its vaults and taking it out after some time. Will the bricks have turned to gold? Of course not. Heavy protection does not affect the quality of the goods you put there.
As for eIDAS, there is no requirement on the assurance level of the identification of the signatory. Identification happens outside the fortress. The quality of the signature is not enhanced just by enclosing the robot in strong protection. It will not exceed the quality of the identification.
The signature robot acts as a proxy, but definitely not for the signatory. The simple reason is that the signatory has zero control over it (and usually has no idea it exists). The signature robot is a proxy for the relying party, the organisation that requires a signature, a government body, for example.
- signatory — the person who signs
- relying party — the business or institution that wants a signature
Unpleasant Security Hole
Genuine qualified signatures cannot be told from forged ones since the link to the signatory is not cryptographically assured – your digital DNA is not used. This means that the whole scheme offers a potential back door for the relying party. It depends on the relying party (the Swedish Tax Agency, for example) to be fair, acting in good faith, and its software to be bug-free. The relying party probably controls the computer code that may cause a qualified signature to be generated for any person, with or without actually involving that person. The signature robot in its fortress generates the signatures it is told to. It is void of any judgment or discernment.
It should be noted here that the Swedish Tax Agency has earned the respect of the Swedish public as fair and acting in good faith. These are good times. How about bad times? The potential back door will still be there and may be exploited.
How come an infrastructure with such weaknesses draws so little criticism? That will be the subject of the next post.
Comments are closed due to the spam factor. You may respond by email to
blog AT soderstrom DOT se
